Read Next
How Identity Protection Tools can Save You Time, Stress, and Money.
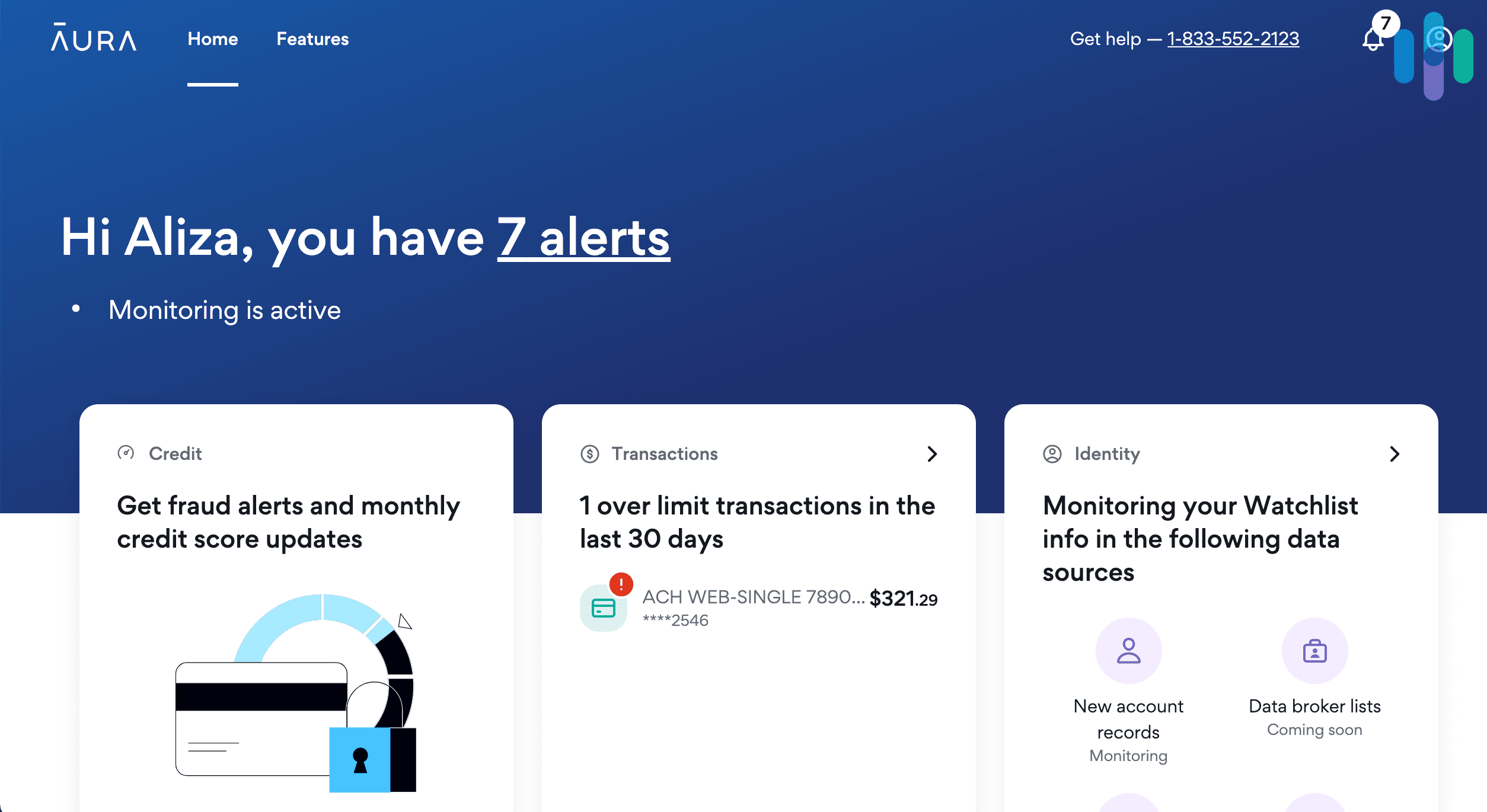
Once they have methods to contact you, somebody can send you a counterfeit message concerning suspicious activity...
Published Feb 12, 26
5 min read
More Posts
Navigation
Home
Latest Posts
How Identity Protection Tools can Save You Time, Stress, and Money.
Published Feb 12, 26
5 min read
3 Easy Facts About Identity Protection Tools Explained
Published Feb 10, 26
5 min read
Identity Protection Tools for Beginners
Published Feb 08, 26
5 min read